‘Stop, look and listen.’ This was the safety mantra of the ‘80s in an attempt to curb the number of car accidents involving young pedestrians. Everyone knew those three simple words, everyone played them back in their minds each time they came to cross the road, often well into their 20s and 30s. It was an ad campaign so successful it averaged a 20% reduction in road accidents in and around school zones.
Now that the children of the ‘80s are grown and hold important positions such as teachers or resource producers for successful websites, these lessons from our childhood remain entrenched in our thoughts and actions. Perhaps it’s time we give a little more thought to the ‘Stop, look and listen’ of the current generation of young people.
Listen to experts weigh in on cyber safety on our podcast, For the Love of Teaching.
What trends are we seeing now which we must put an end to, to prevent a legacy of long-lasting damage for the kids of today? The ‘80s was a time when the number of cars on roads was increasing at an exponential rate. It became necessary for advertising campaigns to warn of the new dangers associated with the volume of cars on roads. Comparatively, online technologies have now become so ubiquitous that being ‘connected’ is the new traffic we should be concerning ourselves with.
Young people of today need a new mantra, one which highlights the dangers and safe ways of navigating online communities.

How to Teach Cyber Safety to Kids
Let’s look at the word ‘cybersafety’. I have discussed the term ‘cyberspace’ before in a previous blog about Digital Learning in the Classroom, so without going into too much detail again, ‘cybersafety’ can be defined as the ability to navigate and utilise technology in a safe way. When we look at the term with regards to our young people, it becomes necessary to ask ourselves, what are the dangers that they will need to be able to navigate around safely?
To repeat this worn out analogy, how can they stop, look and listen when they are online?
In keeping with the rule of three, I present three key areas which kids of today will need to be familiar with and have ingrained in their minds each and every time they connect to any online community.
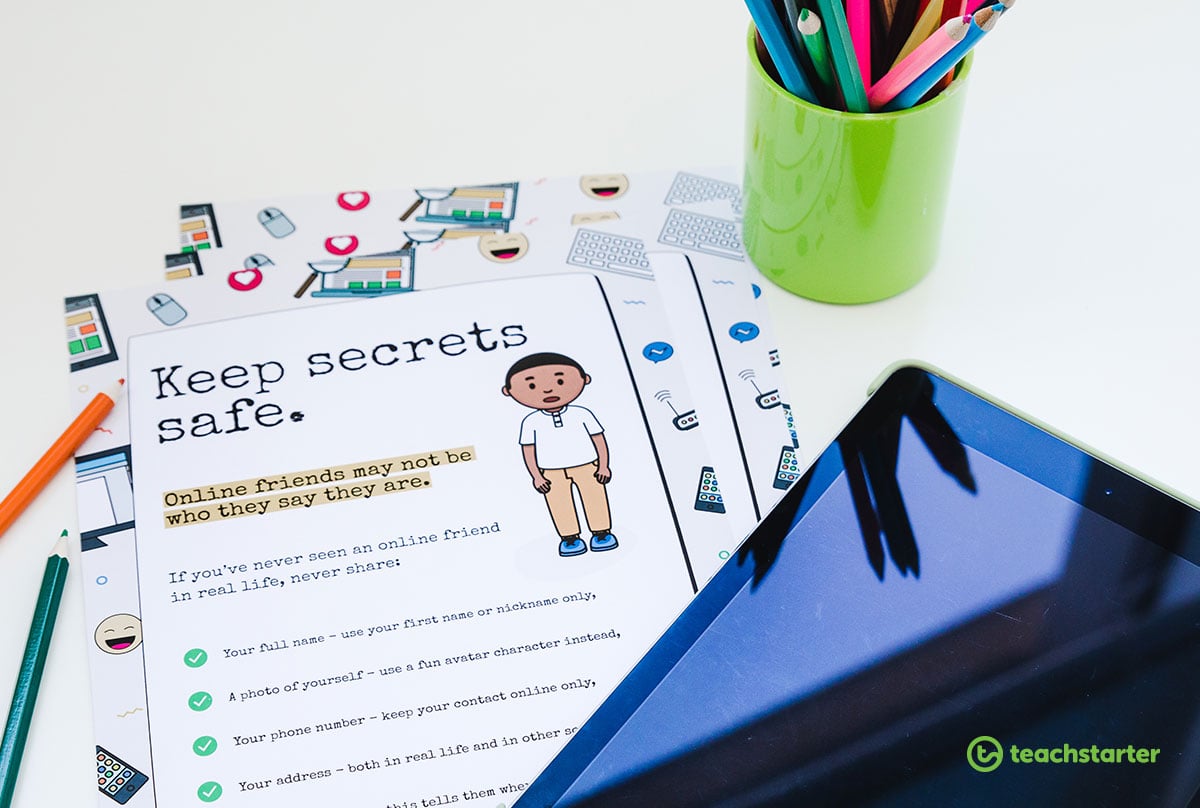
Identity and Privacy – Keep Secrets Safe
Perhaps the greatest risk to young people in online communities is allowing their real world lives to become public knowledge. Privacy, while online, must become second nature to everyone who uses the internet, with children being the most vulnerable.
I think this is best explained by using a scenario:
Hugo is a 9-year-old student who has joined an online gaming community. During a game, a player with whom he has become online friends shares his social media site account and asks to be ‘friends’ with Hugo. Hugo does this as he also has an account with the site that his parents had given him consent to have.
This seems like a fairly innocent online interaction. In this child’s mind, his actions are similar to a real life situation such as meeting someone his age playing soccer, making friends and inviting that person over to his house to play. That is because ingrained in his brain, through hundreds of thousands of years of evolution, is the ability to be a social animal. The problem with this scenario in an online situation is that there are many real world clues that are missing from the interaction which the human brain has not become evolved enough to be able to understand.
Hugo cannot see or hear the person he is interacting with. All mammals react to one another with gestures, sounds and facial expressions and humans are no different. Without these, the human brain fills in the gaps with assumptions which can often be very short of the mark when it comes to reality.

Getting back to our scenario, because I like happy endings, Hugo was lucky that the person he met online was being honest and was someone just like him. However, It could have easily been someone sinister who was then able to see his social media account, his friends, where he lived, where he has been, places he frequents, parents’ work hours, school address, route he walks or buses home and myriad other tidbits of information people inadvertently give away online through subtle details in their posts.
‘Ban kids from using the internet!’ cry some of you, ‘Stricter control over the internet!’ shout others, if only the answers were so simple. But the truth is, the internet is here to stay, it’s becoming a truly massive part of everyone’s lives and is not looking like slowing down.
Any measures we put in place which limit internet use and access are not helping young people, and would probably cause them more harm than good. Bans and strict controls make things more powerful. The current term for this is the Streisand Effect and yes, this is named after Barbra Streisand. In 2003, Streisand discovered the California Coastal Records Project had inadvertently photographed her Malibu mansion as part of its records to preserve the California coastline from erosion. She attempted to sue the photographer as the photo was online. At the time of the lawsuit, the photo had been viewed a total of six times, two of those times by Streisand’s lawyers. When news outlets heard of Streisand’s rage they reported on the image which quickly grew to well over a million views and once the Associated Press reprinted the photo, the number of views became countless.
To be honest, even I have now seen it and I’m sure, by this stage, many of you readers have, too. No one cared about seeing Streisand’s Malibu residence until they were told they weren’t allowed to see it. Banning kids’ access to the internet is a sure fire way to make them seek it out more. What we should be doing is educating them on the best practice methods for managing their online lives.
How do we go about making sure kids know to keep their identity anonymous and ensure personal privacy when interacting online?
Just like the Stop, Look and Listen campaign, we need to make sure kids are aware of the rules and can remember them easily.
- Download the Keep Secrets Safe poster from Teach Starter and display it prominently wherever children are using online technologies. Unpack the poster for your class, going through each step and making sure they understand, not just the rules, but why the rules are important.
- Invent an activity for students to create their own anonymous online identity with a nickname and fun avatar. The Teach Starter Student Avatar Maker is a great alternative to using a personal photograph and there are various random name generators online for students who are finding it difficult to pick a nickname.
- Another great resource for children to help them understand why anonymity is important online are the Hector’s World video clips.
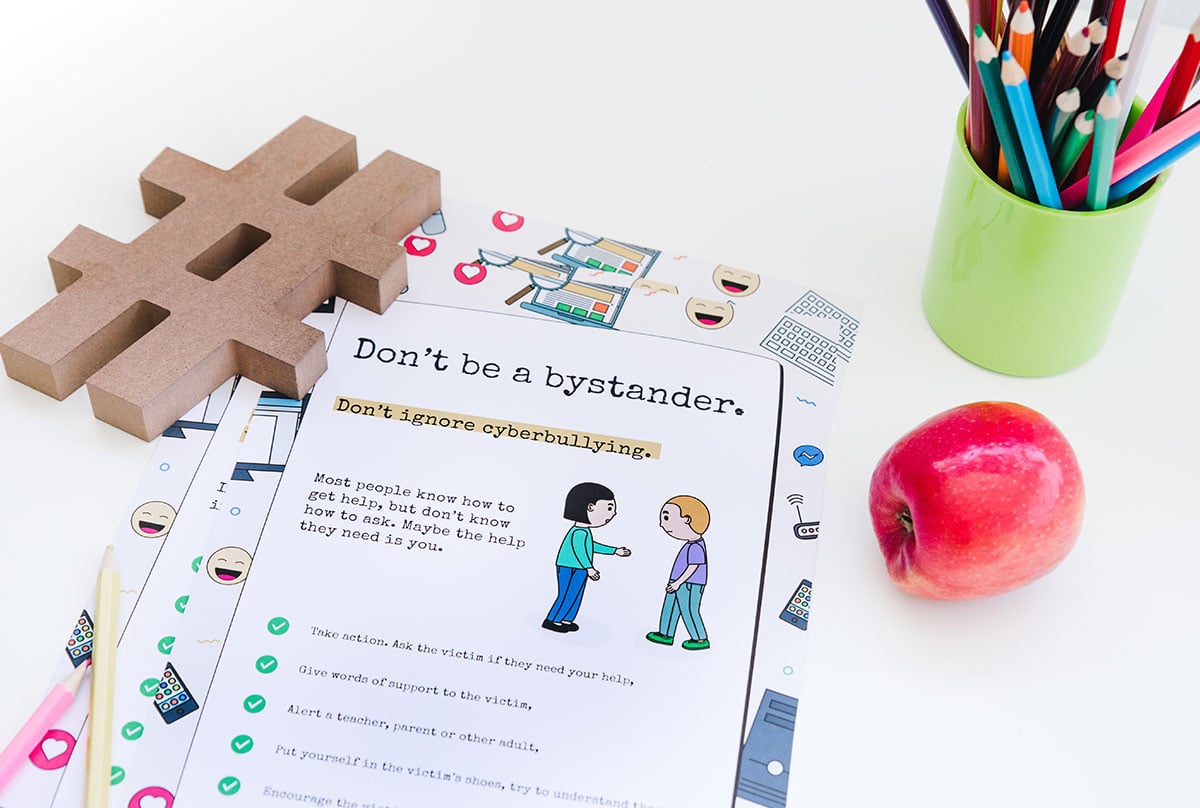
Bullying Awareness – Don’t Be a Bystander
In my classrooms, ‘Don’t be a bystander’ has been the most effective anti-bullying tool implemented, both online and offline.
It breaks down the distinction between being a tattle-tale and helping someone out so that it isn’t just black and white. The strongest weapon a bully has is the ability to stay hidden from those who will bring them to justice, and this is far easier to do online than in real life. The idea behind not being a bystander is to speak out if you see or hear something. It is important that students know they will be heard and listened to if they encounter a situation which is causing another person pain or anguish. What is difficult is making young people understand that ‘speaking up’ and ‘telling on someone’ are not the same thing. The best way of doing that is to show them that being a bystander is just as bad as being the bully.
The different forms of bullying can be described as falling into three categories:
- verbal
- social
- physical.
You may think that ‘physical bullying’ cannot exist in a cyber-sense, however, the threat of physical violence can. These three forms can then be categorised into two distinct states: direct and indirect.
Direct bullying occurs between the bully and the victim and stops there. Indirect bullying is far worse and involves a larger web of people, making it very dangerous in an online sense.
The power of indirect bullying comes from the spread of a rumour, repeated insults from numerous sources, and an attempt to damage the victim’s social reputation. This is where being a bystander comes in for cyberbullying. Another term which came out an Edith Cowan University study is ‘covert bullying’. This refers to long-term bullying which targets an individual through a slow process of undermining their self-esteem and peer relationships. When individual instances are brought to light, the bully can pass it off as being a joke or using sarcasm, whereas the big picture paints a much darker pattern of bullying behaviour.
So how is being a bystander just as bad as being the bully?
Because the bystander becomes the bully’s source of power.
Let’s look at another scenario:
Isaac is an 11 year old student at a school which has embraced a 1:1 iPad classroom setting. While the school has strict rules regarding the use of instant messaging, his entire class still uses it out of school hours. One night, Isaac notices an anonymous account posting messages about Will, a friend of Isaacs. In one message the anonymous poster teases Will about being the teacher’s pet and liking the teacher romantically. Isaac responds to the post by adding the ? (face with tears of joy) emoji into the reply box.
In this instance, Isaac has just justified and strengthened the bully’s original comment. For the bully and the rest of the audience, Isaac has just approved, agreed with and promoted the comment as amusing. More importantly, it has reduced Will’s social reputation, embarrassed him and alienated him from his classmates. Again, because I like happy endings, Isaac thinks before he posts, he decides that the emoji is not going to help the situation and instead deletes it and ignores the post. This simple action prevents the snowball effect the offhanded emoji would have caused; the bully’s comment loses power. Isaac instead realises that no one is there to support Will so he tells his mother what is happening and asks if he can call Will to check on him.

The next day, Isaac and Will approach the teacher to alert them to what is happening and to get Will some help in dealing with the situation. When the teacher raises the issue in class, many other students also report similar occurrences and Will begins to feel like he’s not alone in feeling targeted. The above scenario and following events are a textbook case of how to take actions and not be a bystander.
Teach Starter’s Don’t Be a Bystander poster highlights all the steps Isaac took and is a great visual aid tool to display in your classroom.
Once it becomes clear to the children that taking action in the right direction can prevent bullying from taking place, they will no longer perceive it as tattling, but instead, it will instill in them a sense of justice when dealing with cyberbullying. For a great resource, take a look at this Teach Starter Cyberbullying lesson, part of the Bullying and Resilience Unit of work.
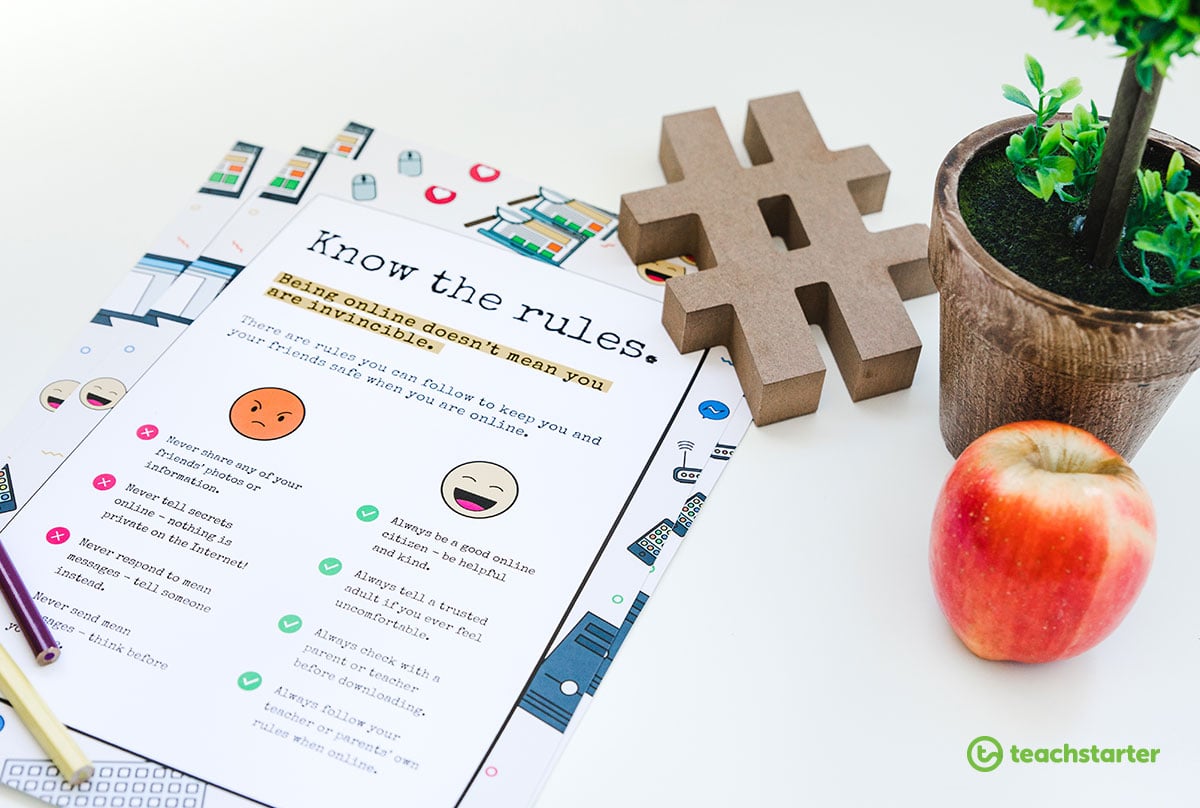
Know the Rules – Think Before You Post
Look before you leap! Consider the consequences. In this age of cultural impatience and instant gratification, of unintended tweets and misinterpretation, today’s young people more than any generation, are quickly losing the art of social prudence.
People with high social prudence scales are less likely to offend others and strongly believe negative consequences occur unless they pay attention to what others think about them. Conversely, those with limited social prudence rarely take into consideration that their actions towards others may affect them personally and are more likely to speak their mind without judging possible ramifications. The internet has exacerbated this phenomenon exponentially by anonymising or at least distancing people in such a way that consequences virtually disappear in the eyes of many young users. Unfortunately, we cannot seem to get away from the kind of online nastiness this can breed, we can, however, educate to prevent these behaviours in young people and just as importantly, avoid exposing young people to these behaviours in others.
From my classroom experiences, social prudence in an online situation can be very removed from a person’s social prudence in real life. I attribute this to good parenting and schooling in preparing young people for the society of the real world. In contrast, there is virtually no skills training for interacting in the online world for anyone. This needs to change, otherwise we are essentially bringing children into an online world with no concept of inherent rules, filters or expected behaviour parameters.

Allow me a final scenario if you will:
Kylie is 8 and has been given access to the library computer to undertake Genius Hour research on whales and plastic in the ocean. She discovers an online forum where people can discuss issues relating to the environment. After she posts her question, another user attaches a video to their conversation for Kylie to download and watch.
Despite how uncomfortable this kind of situation makes us feel, it is an all too common one. Kylie felt like she wasn’t doing anything wrong, in actual fact, she may have thought she was very clever to be getting the information this way. In this reversal of roles, we see how people can easily become victims of those with low social prudence. Despite acting in a way she thought was right, Kylie inadvertently allowed herself to be in a position of vulnerability. In this case, however, Kylie has been taught that she should never download anything without asking for permission.
A happy ending ensues when Kylie, through consultation with the librarian, downloads a whale watching video which is perfect for her presentation. The librarian knew the forum was reputable as it had the .edu tag in the URL and screened the video before Kylie saw it.
The Teach Starter Know the Rules poster has a set of basic, easy to understand online rules which you can display in the classroom to remind students of the best practice methods when interacting online. In the above scenario, Kylie followed only one of the simple rules outlined, but it saved her the possibility of being subjected to the actions of someone with ulterior motives.
From an early age, we are taught to say please and thank you, to be courteous and to chew with our mouths closed. Our real world interactions are governed by the manners we are taught by parents, carers and teachers. Similarly, we are taught not to talk to strangers, to stop look and listen before we cross the road, and to not run with scissors, simple rules which must be learned for our safety and well being. It is vital that we are giving similar online skills to our young people in order for them to act appropriately online and to maintain safe online behaviours.
Cybersafety is for everyone.
We have warning pamphlets and advertisements for new users of technology aimed at the over 50s, constant security updates for virus software, scam alerts, nigerian prince jokes, fake news, foreign spies, the internet is a minefield. Yet, the internet is also an amazing place, a wonderful utopia of seemingly endless knowledge, interesting and diverse communities and technologies which will amaze and astound you. We would be remiss if we didn’t bring this wondrous marvel of the 21st Century into the lives of our young people. But as with anything, approach with caution, be a decent citizen, and learn the rules.
Once young people learn the ‘stop look and listen’ on the internet, the online world is their oyster. Download our set of Cyber Safety posters for the classroom.






Comments